|
"A
receiving application is assumed to have been programmed to be aware of only
those constructs of a particular version of UBL. It would therefore be deployed
with the schemas for that UBL version and will typically employ validation of
received documents in advance of acting on the semantics represented by the
information structured and identified in the XML. The application receiving an
instance of a later UBL version may find either unrecognized constructs or
recognized constructs in unexpected places. For example, a UBL 2.5 application
would not recognize constructs introduced by the schema for UBL 2.7.
Shown
previously in figure 1, UBL 2.1 describes a two-step
validation processing model. The first of these two steps confirms the
structural and lexical constraints (the lexical being, effectively, the
structure of the content) of the document. The second step confirms the value
constraints being imposed by business requirements beyond the purview of the
committee, but within the context of using UBL between trading partners. At
either stage of validation, a failure indicates that the message is to be
rejected, either because the document structure or value constraints have been
violated.
This
processing model for like-versioned UBL systems does not serve a UBL 2.5
application receiving a UBL 2.7 instance with unexpected content.
Figure 2
illustrates a customized processing model
that
supports forward compatibility of UBL instances. This augments the published processing
model in figure 2.1.
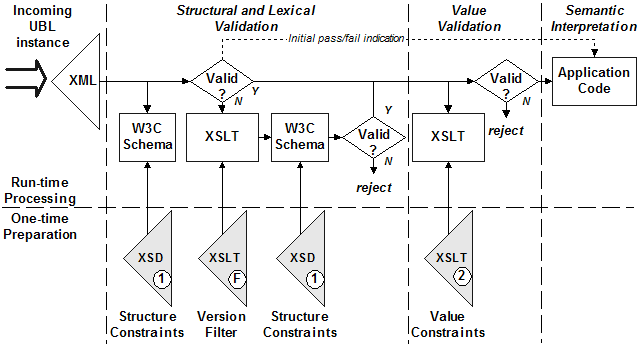
Figure 2:
A customized processing model supporting forward compatibility (Diagram
courtesy of Crane
Softwrights)
This
customized processing model for the receiving system uses only that version of
UBL schema supported by the receiving system, and does not involve any
inspection of the XML instance in advance of validation. In this model an
initial schema validation failure indication is recognized to possibly have been
triggered by an instance using features added in a schema later than the version
supported by the system. After such a failure, an instance pruning process takes
away unknown constructs from the instance being validated. The resulting pruned
instance can then be checked for schema validity. If successful, the pruned
instance is passed to the second stage value validation.
As
with the published model, passing value validation grants delivery of the
instance to the application. In this model, a second piece of information
accompanies the instance being passed to the application. The application can
already assume that value constraints in the document are satisfied. An
"initial pass/fail" indication tells the application that the instance
it is working with satisfies the structure constraints in either an unmodified
("initial pass") or a modified ("initial fail") state.
An
unmodified instance can be acceptable for business processing regardless of the
stated version number found in the UBLVersionID element if all of the business
objects found in the instance conform to the constraints of the application,
unused additions in a later version notwithstanding. The application can use
out-of-band decision making, including the UBLVersionID element as input, to
accept or reject a modified instance for the purposes of doing business.
In
both cases if the instance is delivered to an application, such an application
relying on schema validity for inspecting instance content can successfully
extract any information therein.
Considering
the example above, a UBL 2.7 instance without constructs unrecognized by the UBL
2.5 schema would validate using the receiving application's schemas. The
instance would be passed to the UBL 2.5-aware application untouched and with an
"initial pass" indication. In this case that the instance is marked
2.7 is irrelevant. A UBL 2.7 instance with unrecognized constructs would fail to
validate with the UBL 2.5 schema and would be passed to the application after
being pruned to the UBL 2.5 subset and with an "initial fail"
indication. In this case that the instance is marked 2.7 is relevant to the
application and user deciding how to proceed.
In
support of this customized processing model, instance pruning processes for UBL 2.0 are
already publicly available [Crane
Resources]. Such processes are programmatically derived from the UBL
specification rather than being hand-coded. This approach gives the pruning
process a higher level of assurance of accuracy than coding the filter by
hand." (Source: Crane Softwrights' "Versions in UBL")
MXV
optionally generates Windows command files supporting the customized processing model
for forward compatibility (figure 2). See next
chapter for MXV pruning processes.
|


![]() © Copyright 2011 Data Management Solutions, Wellington, New Zealand
Last Update: 2012 November 28
© Copyright 2011 Data Management Solutions, Wellington, New Zealand
Last Update: 2012 November 28